This analysis examines the full spectrum of operations behind the American-Israeli strike on Iran beginning February 28, 2026, from long-term cyber infiltration and network compromise to coordinated military strikes on key Iranian sites. Drawing on open-source intelligence, technical indicators, official statements, and published reporting, it reconstructs the complete kill chain and maps the physical and digital targets systematically dismantled.
1. Background and Strategic Context
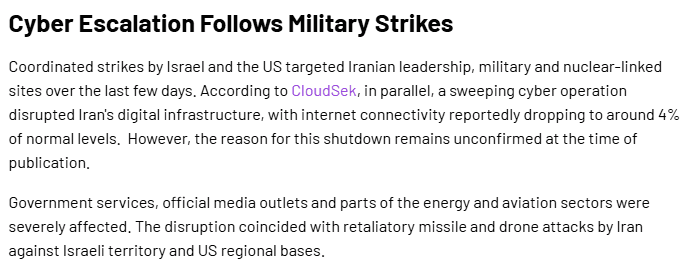
In the last week of February and the opening days of March 2026, Iran was subjected to an intensive campaign of cyberattacks. There has been no official word from the United States or Israel confirming that cyber effects were brought to bear in the first 48 hours of the conflict, though there have been reports of cyber activities inside Iran having taken place.
The massive paralysis did not happen overnight, but lasted for several months. The result of careful planning and execution reveals the complete Kill Chain.
2. The Buildup: Months of Preparation
2.1 Strategic Preparation and Long-Term Infiltration (Pre-December 2025 – January 2026)
In the months leading up to the operation, US and Israeli cyber forces conducted extensive strategic preparations targeting Iran's critical infrastructure. This involved long-term infiltration of the country's energy sector networks, allowing attackers to map vulnerabilities and deploy dormant malware deep within Industrial Control Systems (ICS) and Supervisory Control and Data Acquisition (SCADA) systems. Reconnaissance efforts focused on identifying weak points in grid synchronization protocols, pipeline valve command structures, and the satellite communication frequencies relied upon by energy facilities. Cyber units coordinated closely with electronic warfare assets to ensure synchronized execution, while trigger mechanisms were carefully developed to activate malware at the precise moment physical strikes would begin, maximizing destruction and paralyzing any coordinated response.

Supply Chain Attacks
The United States and Israel conducted supply chain attacks, infiltrating maintenance channels of Western and Indian equipment suppliers that Iranian energy companies depend on. This established covert communications and intelligence networks inside Iran, effectively planting "digital lurking forces" and "timed explosive devices" within industrial control systems.
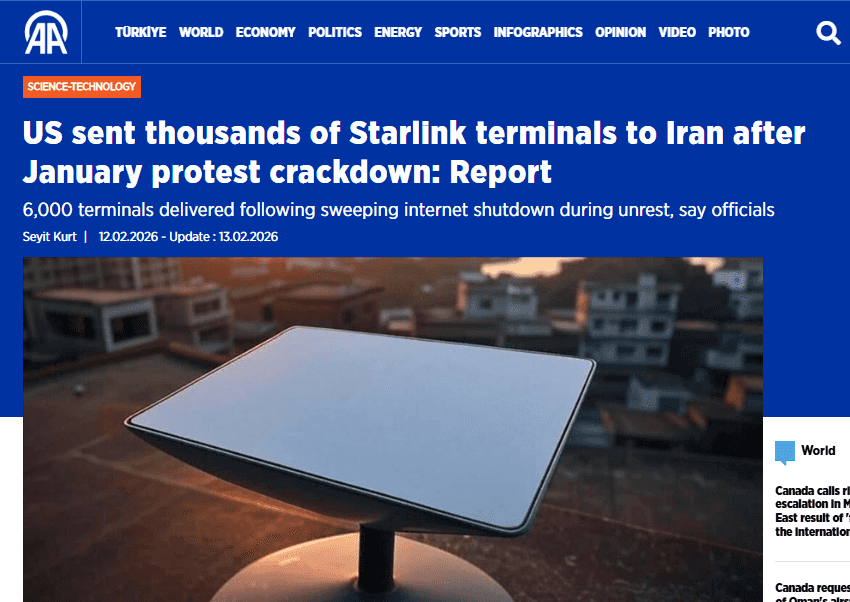
Starlink: Digital Bridges Through Network Blockades
Simultaneously, the US secretly shipped nearly 7,000 Starlink terminals to Iran through covert channels, with President Trump fully aware of the deliveries. Beyond helping civilians bypass the national firewall, attackers exploited Starlink terminal vulnerabilities to further establish hidden communication pathways. When ground communications are severed, a resilient satellite network becomes the ultimate high ground for information warfare.
Strategic Coordination
Cyber units coordinated with electronic warfare assets to ensure synchronized execution, with trigger mechanisms set to activate malware precisely when physical strikes began.
2.2 Tactical Testing (January 2026)
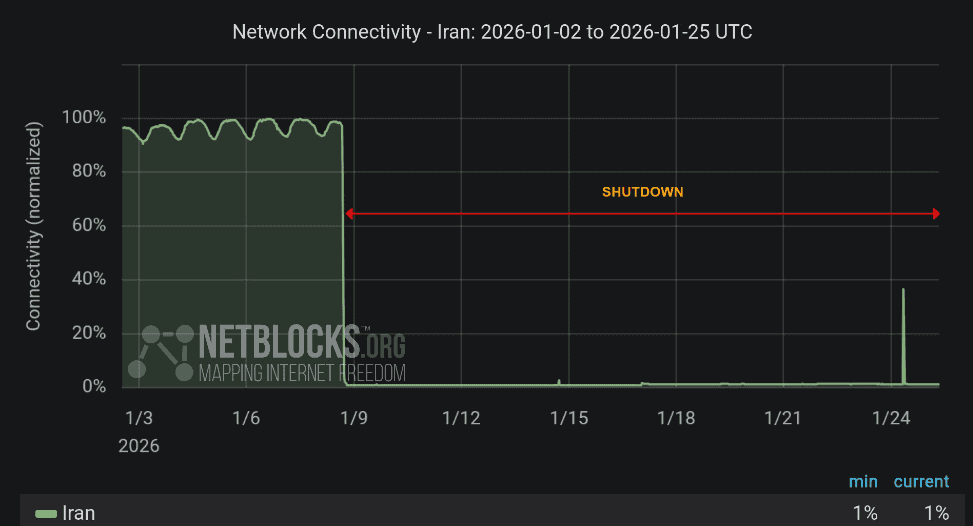
During protests that forced the Iranian government to impose a nationwide internet shutdown, US-Israeli cyber forces seized the opportunity to conduct real-world testing. As Iran's national network and energy industrial control systems buckled under the blackout, attackers probed for vulnerabilities and mapped emergency response mechanisms, effectively using the chaos as a live-fire exercise to calibrate their final assault. This directional positioning allowed them to refine targeting coordinates with precision, ensuring that when the physical strikes came, every logic bomb and malicious payload would hit its mark with devastating accuracy.
2.3 Early Probe Attacks (February 2026)
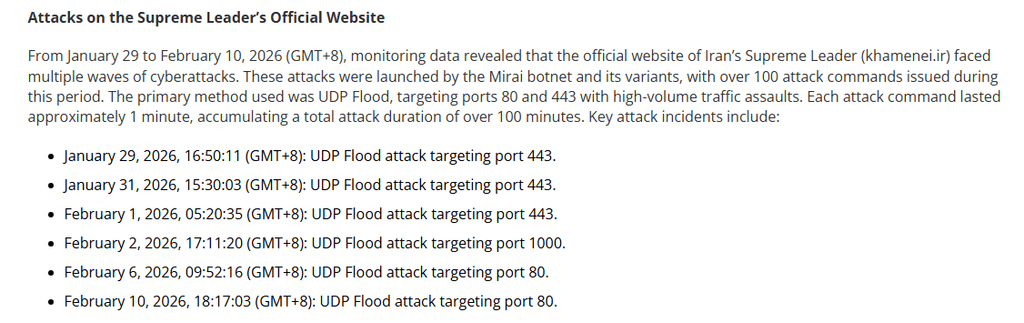
- On February 4, 2026 (GMT+8), NSFOCUS detected a DDoS attack on the Iranian news website www.tabnak.ir. The attack was launched by a new variant of the Mirai botnet.

- On February 20, 2026 (GMT+8), monitoring detected a DDoS attack on Iran's National Smart Government Services Portal (my.gov.ir).
- Reportedly, there were also several attacks launched on Iran’s Supreme Leader’s official website
2.4 Fixed-Point Preset: Precision Pre-Positioning (February 2026)
With critical nodes of Iran's energy system already identified, US-Israeli cyber operatives moved to the next phase: precision planting. In confirmed key locations, such as power grid dispatching centers and pipeline PLC controllers, they pre-positioned remotely triggerable "logic bombs." These malicious payloads lay dormant, embedded deep within industrial control systems, awaiting activation. When the moment came, they would not merely disrupt but systematically dismantle the infrastructure from within, transforming Iran's own energy networks into weapons of paralysis.
3. The Attacks
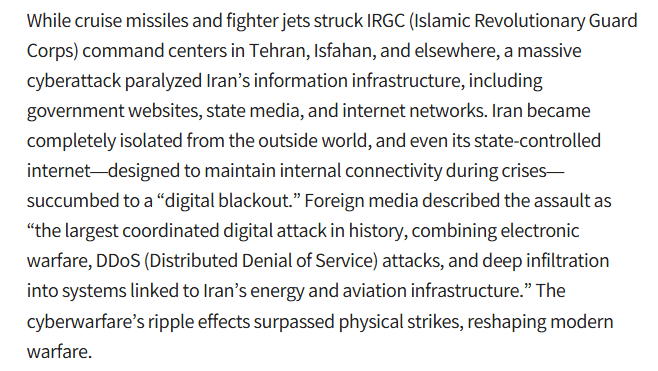
3.1 Primary Target: Iran's Energy System
The main target of the cyberattack was Iran's energy system, encompassing the national power grid, oil pipeline control systems, refinery production facilities, and the satellite communications networks that tie them together, as well as basic communications infrastructure and internet connectivity. To achieve this, attackers employed a multidimensional composite of techniques working in concert.
Layer 1: Targeted Malware Against ICS/SCADA Systems
An updated version of the historical Stuxnet virus was deployed against Iran's Energy Industry Control Systems (ICS) and SCADA systems. This malware remained dormant for extended periods before activating at a predetermined time or upon receiving external instructions, at which point it directly tampered with control instructions or damaged hardware, such as altering grid frequency control commands or manipulating oil pipeline valve operations.
Layer 2: Massive DDoS Attacks
Massive distributed denial of service (DDoS) attacks flooded the energy sector's emergency response systems and network control centers, overwhelming them and collapsing command and coordination capabilities.
Layer 3: Electronic Warfare Synchronized With the Cyber Assault
Electronic warfare was synchronized with the cyber assault. GPS signal interference and electromagnetic suppression targeted specific communication frequency bands, particularly those used by energy facilities. By disrupting the GPS timing signals essential for grid synchronization, attackers directly induced frequency oscillations and chain reactions of protection devices, causing physical damage that compounded the digital destruction.
3.2 Cyberattack on Iran's National Prayer App: "BadeSaba Calendar"
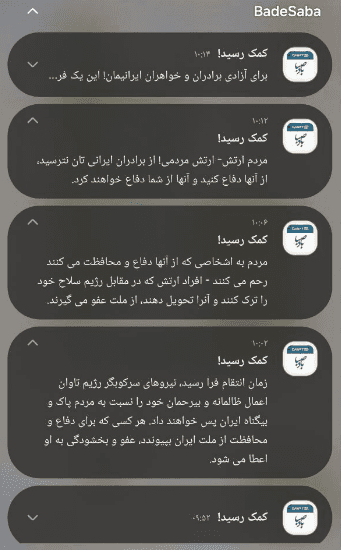
Attackers covertly infiltrated Badesaba's CI/CD pipeline, compromising the build environment and injecting a highly obfuscated payload into a legitimate version update. When millions of users clicked "Update," backdoor programs were silently installed on their systems, a classic supply chain attack that bypassed sandbox detection and allowed malicious code to reside deep within the system.
As the national backbone connection dropped to 4%, a pre-set internal logic trigger activated. The attackers communicated through a low-bandwidth cellular signaling channel or a pre-buried shadow link, sending a wake-up instruction of just a few bytes. This roused a long-dormant malicious payload, which then took full control of the system.
In the communication vacuum across the country, the Badesaba notification service sprang to life, displaying a carefully designed Persian pop-up across millions of screens: "Help has arrived."
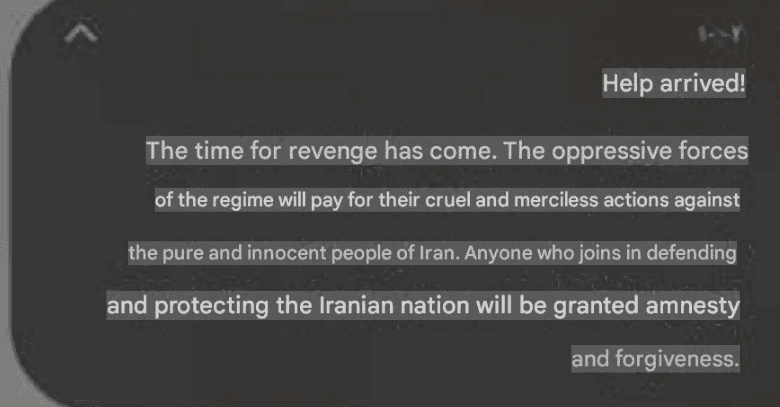
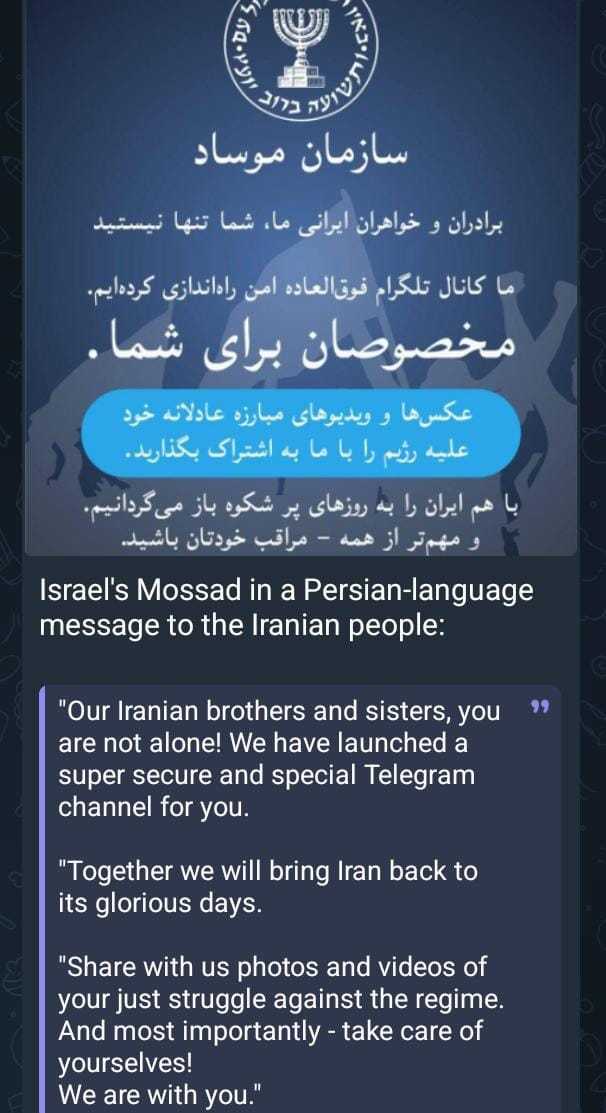
3.3 Messages Sent to the Iranian People by Mossad
During the operation, Mossad sent direct messages to the Iranian people via digital channels as part of the broader psychological warfare and information operations component of the campaign.
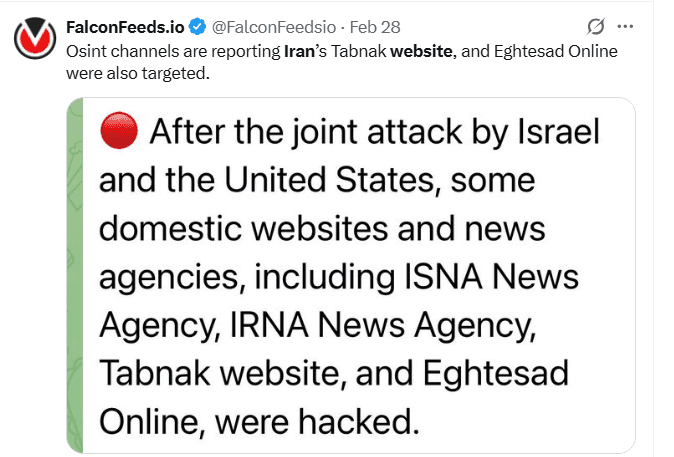
3.4 Attacks on Iranian News Websites and State Media
One of the early targets of the cyberattack was Iran's official media system. A number of news websites were hacked and had their pages tampered with to display various unauthorized information. Reports on Iranian Telegram channels noted that as physical strikes were underway, "a broad wave of cyber activism" had already been launched. Confirmed targets included IRNA (the official state news agency) and ISNA (the semi-official Iranian Student News Agency). This attack on media infrastructure served a dual purpose: to disrupt the government's channels of information while simultaneously paving the way for subsequent psychological warfare.
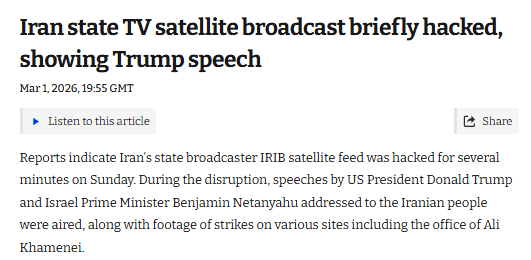
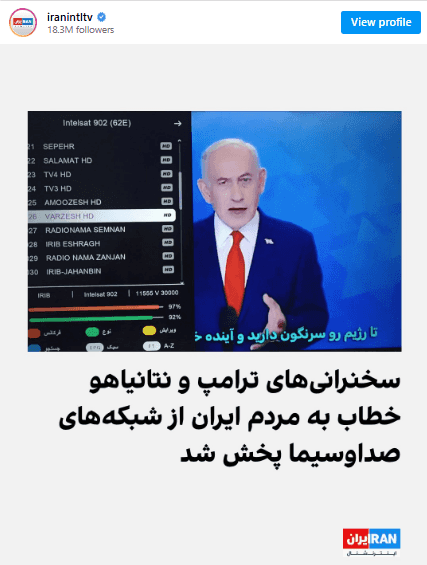
3.5 Television Broadcast Hijacking
Reports indicate that Iran's television broadcast signal was interrupted by a split screen showing President Trump and Prime Minister Netanyahu speaking with Persian subtitles, urging Iranians to rise up against the regime. In a video message directed at the Iranian people, Trump declared: "Your moment of freedom is coming," and called on citizens to "take over your government" once the military phase concluded. The ultimate message of this information warfare campaign is unmistakable: the operation's goal extends far beyond the destruction of military installations — it is aimed at regime change in the Islamic Republic of Iran.
3.6 Network Disruption
The nationwide internet connection rate plummeted to 4%. This was not an ordinary submarine cable failure or a simple DDoS interruption. Based on online reports and OSINT sources, this is a multi-dimensional collaborative "network saturation attack." What the joint US-Israeli command has shown is the double harvesting of the logical layer and the physical layer.
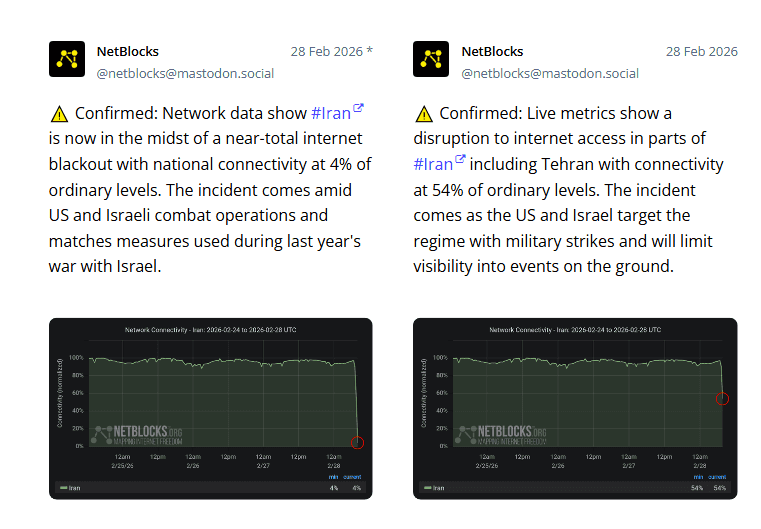
The Logical Layer Attack
The first wave targeted the internet's backbone. The BGP protocol, normally a messenger for routing, became a deadly traitor in the early hours of February 27. Attackers executed massive BGP route hijacking, broadcasting a false best path that, within minutes, funneled all international traffic in and out of Iran into a preset digital black hole. Simultaneous root domain hijacking threw even domestic DNS resolution into chaos, leaving Iran's network lost in a digital maze. The real killer lurked deeper: a long-embedded zero-day in Iran's national intranet authentication system was activated. By tampering with the header logic of communication protocols, the attackers caused gateway devices to crash when processing malformed packets, exposing and weaponizing the firewall's self-protect mechanisms. This turned defensive floodgates into a chain reaction that locked the system down.
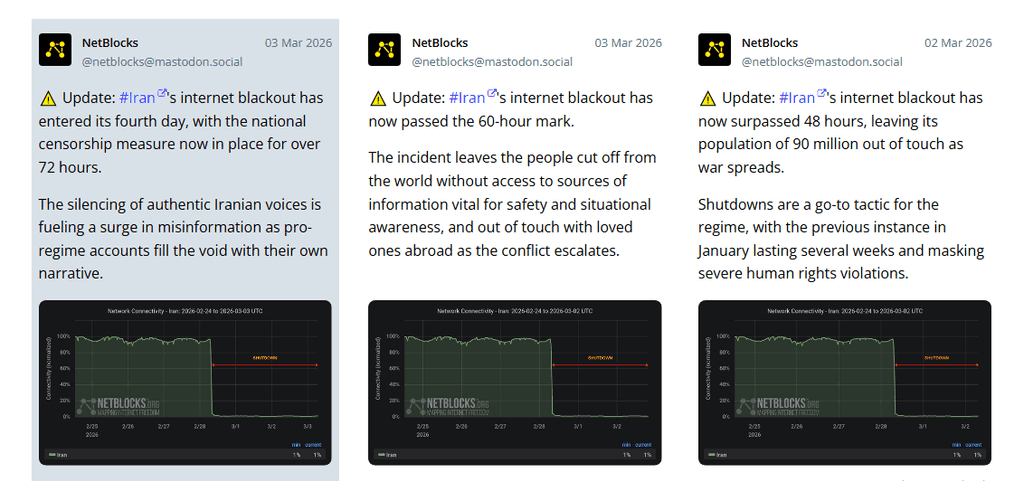
The Physical Layer Attack
Just as the logical layer was paralyzed, the physical attack struck in sync. US EA-18G Growler electronic fighters cut into communication links, using high-power narrow-band interference to disable microwave towers and 5G base stations around Tehran.
3.7 Finance: ATMs and Payment Systems Paralysed
ATMs and payment systems were paralysed across Iran as a result of the cyber operations.
3.8 Transportation: Airport and Air Control Failures
Airport scheduling and air traffic control systems failed, resulting in widespread delays.
4. The Effect of Creating Transparency on the Battlefield
4.1 Blinding Air Defense Systems
The immediate military value of the cyberattack was the systematic blinding of Iran's air defense networks. By paralyzing the power grid that fed radar stations and command centers, and severing the communications and data links they depended on, attackers rendered Iran's air defense system largely ineffective during the initial phase of the operation. Radar screens went dark, early warning systems fell silent, and defenders found themselves unable to effectively monitor their own airspace or mount a timely counterattack against incoming stealth aircraft.
4.2 Breaking the Chain of Command
The collapse of Iran's national communications system created chaos at the highest levels of military and government decision-making. Reliable, real-time communication between Iranian military units and senior leadership, including the supreme command body, became extremely difficult or impossible. The command, control, and intelligence (C3I) system was effectively shattered, meaning that even units still capable of fighting received no orders, while leadership remained blind to the developing tactical situation on the ground.
4.3 Establishing Information Dominance
While Iran groped in the dark, US and Israeli forces operated with near-perfect battlefield awareness. Through months of infiltration and the establishment of unaffected intelligence networks, they achieved complete real-time situational awareness. Iranian forces were rendered fully passive in the information domain, unable to track enemy movements or predict strike locations. This information asymmetry formed the bedrock of the entire operation's success.
The cumulative effect of the above was the creation of a "one-way transparent" battlefield, a concept where one side enjoys complete visibility. This military principle, which first emerged prominently during the 2003 Iraq War, reached new heights in the Iran operation.
5. Operational Timeline
February 27, 2026 (Night) — The Logical Siege Begins US Cyber Command's Defensive Cyber Protection teams fully take over the security protection of the Department of Defense's Information Network (DODIN) and the Department of Transportation. Objective: to prevent Iran from infiltrating or interfering with US command communications in advance and to ensure the stealthiness of force delivery.
Pre-Wave (Cyber Infiltration & Air Defense Neutralization): Before the formation of US and Israeli warplanes entered the Iranian Air Defense Identification Zone (ADIZ), US Cyber Command had deployed malicious code against Iran. Interference against Integrated Air Defense Systems (IADS) was carried out. Unlike conventional electronic suppression (EA), this was logical interference, achieved by tampering with radar signal processing algorithms to create a large number of "false trails" on the defensive side's screens. This forced Iran's air defenses into a tailspin, causing target allocation overload. It became impossible to identify real swarms of stealth aircraft among hundreds of fake targets. This tactic meant that even with S-300 and S-400 hardcore anti-air missiles, the defense could not complete the kill loop because they simply "could not find the real target."
Target Acquisition via Signal Intelligence: The operation's precise destruction of underground bunkers and command centers relied heavily on signal monitoring and traffic fingerprint analysis. By secondary desensitizing location data collected from contaminated applications such as Badesaba, attackers reconstructed the high-frequency activity trajectories of key Iranian military personnel in cyberspace. This mobile-based signaling positioning offered accuracy far exceeding traditional satellite reconnaissance, allowing real-time location of active areas within underground bunkers. This provided the most accurate impact coordinates for drilling munitions such as the GBU-57.
February 28, 2026 — 01:15 (Start of Action) First Strike: Tomahawk cruise missiles and B-2 bomber raids begin. Cyber Mission Force suppresses or deceives Iran's military communications and radar early warning systems, causing them to display false air information or to completely disable them.
Armed with intelligence derived from signal monitoring, precision strikes targeted underground command centers and military installations. The coordinates ensured that munitions hit exactly where personnel were concentrated, maximizing the destructive impact of the physical assault.
After the physical strike, the cyberattack shifted to causing secondary damage to the infrastructure of the targeted region. US-Israeli cyber forces launched targeted attacks on Industrial Control Systems (ICS) at the damaged military installations. By remotely locking ventilation systems, power adjustment devices, and automated sealed doors, the attackers prevented post-disaster repair of the damaged facilities. This "logic lock" not only expanded the effect of the physical strikes but also completely paralyzed a large number of command nodes buried deep underground through system replication.
February 28, 2026 — All Day (Multiple Waves of Airstrikes) Airpower: More than 125 aircraft participated in the strikes, including 75 refueling aircraft to guarantee a long-range assault.
Cyber warfare continues. EA-18G Growler implements full electronic warfare suppression, and the NSA signals intelligence department monitors Iran's command communication channel in real time to assess the effect of strikes.
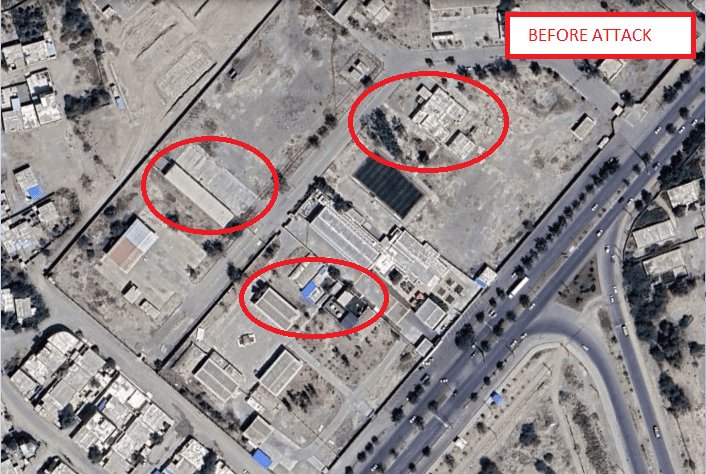
- Attack on Shajareh Tayyebeh” (The Good Tree) school in the city of Minab in southern Iran, a terrible war crime

- Attack on Iran’s Supreme Leader’s compound in Tehran


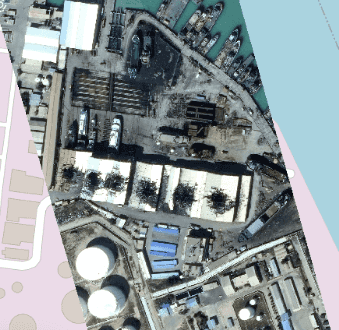
- Konarak Port strike

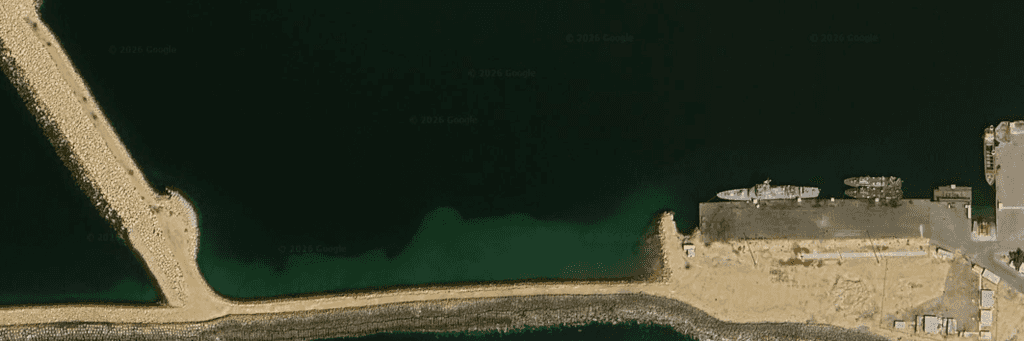
Smoke can be seen rising from the location
March 1, 2026
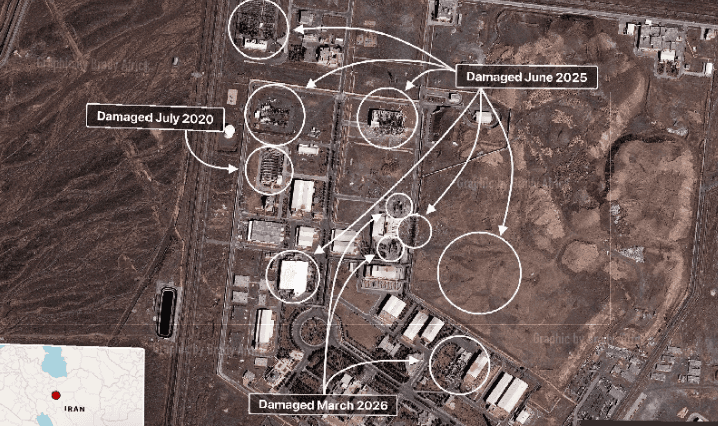
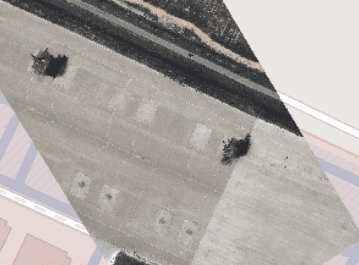
- Natanz Nuclear Site Attack (satellite image published by Vantor)
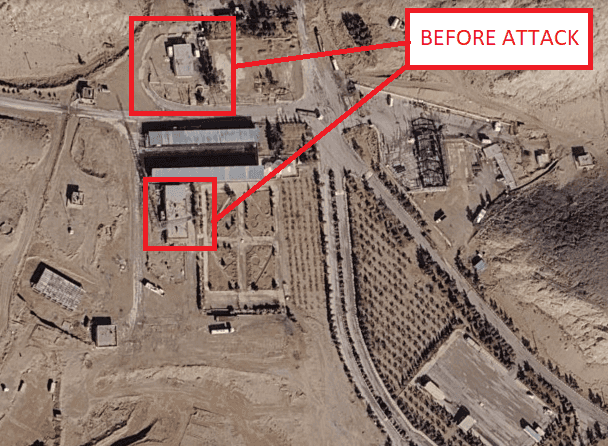
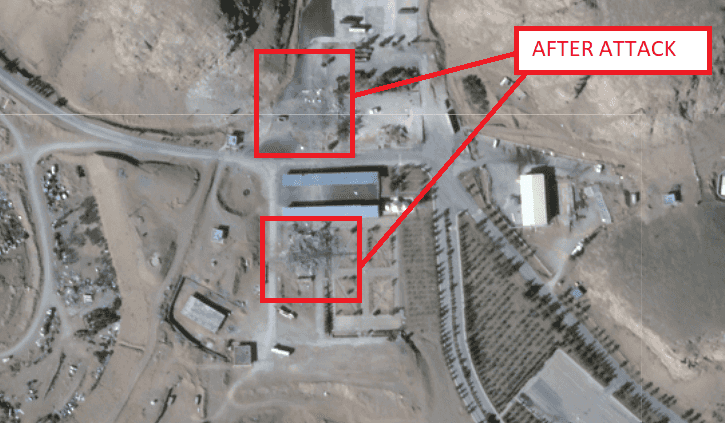
The image below shows undamaged sites prior to the attack (March 2026)
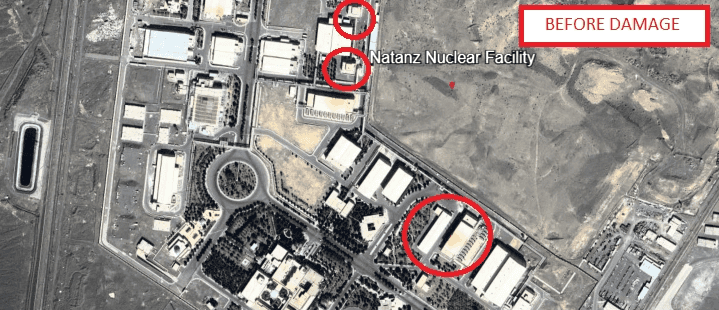
The entrance and exit buildings of the underground fuel enrichment plant in Natanz, Iran were hit and significantly damaged.
- Zahedan airbase attack


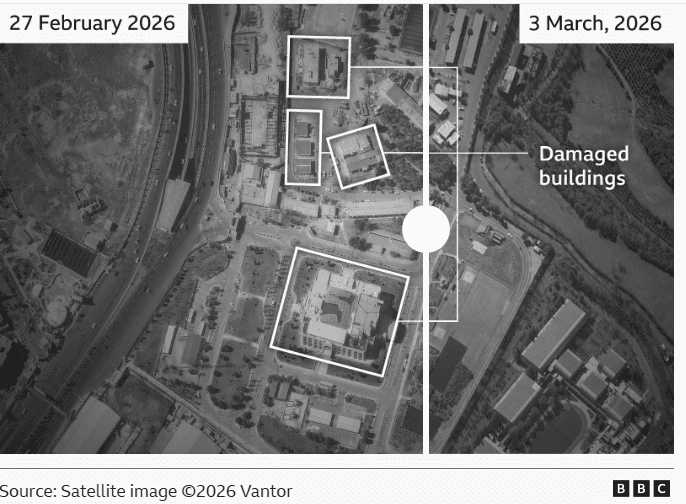
- IRGC Sarollah HQ attacked

IRGC Sarollah (“God’s Revenge”) headquarters in located in Tehran. Buildings within the elite complex were responsible for protecting Tehran’s government institutions and suppressing internal dissent. The Sarollah unit is a key element of Iran’s internal security, tasked with safeguarding the capital and responding to protests or unrest.
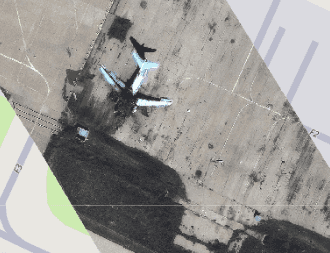
- Tabriz airport attack
Two Iranian F-5 and F-4 fighter jets at Tabriz airport were struck in western Iran as they were prepared for takeoff
March 2, 2026
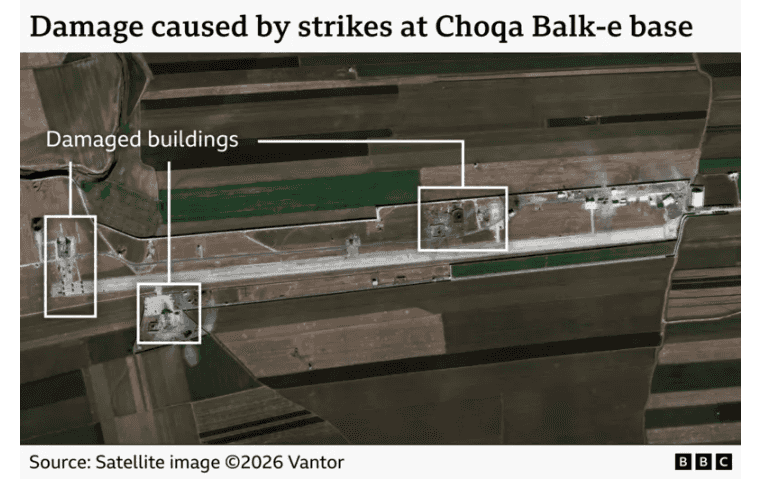
- Choqa Baulk-e Alireza drone base attack
- Bandar Abbas harbour airstrike, in Hormozgan Province


March 3, 2026
- Attack on IRGC HQ in Tehran
- Large damage to key buildings at a Naval base in Bushehr, Iran
- Attack at Isfahan North missile base
- Iran Police Headquarters attack
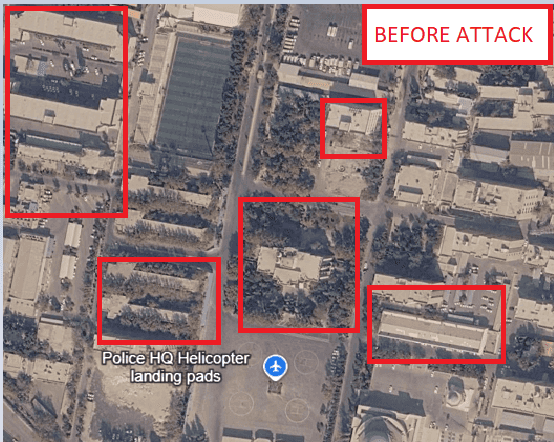

Large damage at the Islamic Republic of Iran Police Headquarters in District 3 of Tehran. Other police facilities in the city were also struck as part of a broader campaign targeting internal security infrastructure.
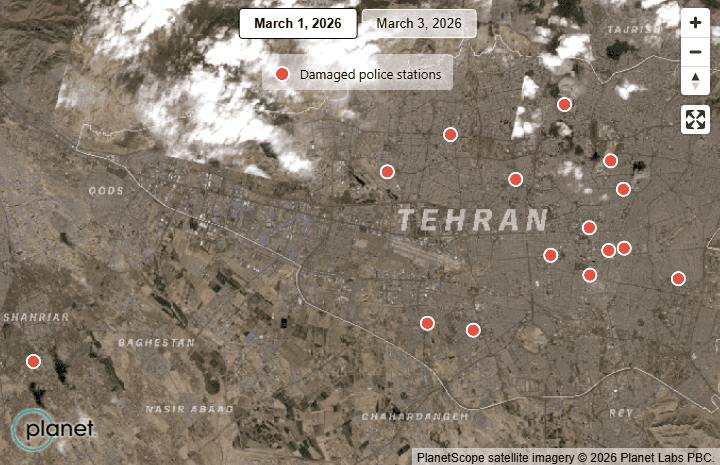
(Posted by Bellingcat)
MARCH 4, 2026
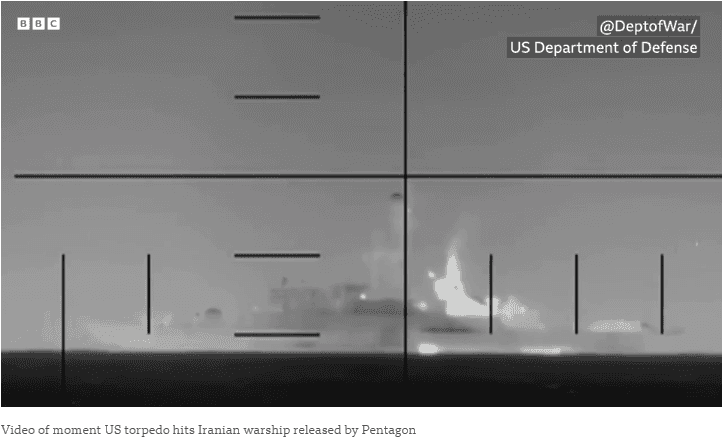
- The IRIS Dena was the newest destroyer vessel in Iran’s naval fleet, and was commissioned as part of Iran’s domestically-produced Moudge or Mowj class multi-role guided missile frigates in 2021. The warship featured anti-ship missiles, surface-to-air missiles, torpedo launchers, machine guns, and a cannon. It was torpedoed by a U.S. nuclear submarine.
March 5, 2026
- A large fire visible from in Bushehr International Airport, Iran.

- Attack on Iranian Emergency Medical Base in Shiraz
MARCH 6, 2026
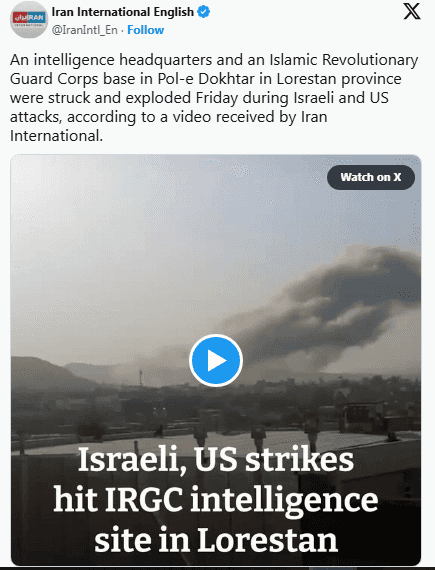
- US and Israeli airstrikes hit an IRGC intelligence site in Lorestan
MARCH 7, 2026
- Mehrabad airport attack

Images below show airport before attack


- US hit desalination plant on Qeshm Island
A US attack struck a freshwater desalination plant on Iran’s Qeshm Island, disrupting water supplies in 30 villages
MARCH 8, 2026
- Attack at a Military Garrison, Isfahan, Iran

- US, Israel hit five oil sites in and near Tehran
6. CENTCOM's Weapons List and the "Special Capabilities"
On March 1, 2026, US CENTCOM released a rare list of weapons and equipment for Operation "Epic Fury" on platform X and officially confirmed the existence of "special capabilities" for the first time but they didn't list them. Strategic intent: to deter Iran and show US military all-spectrum operational potential which is not only accurate but also makes your systems invisible, unconnected and unable to fight.
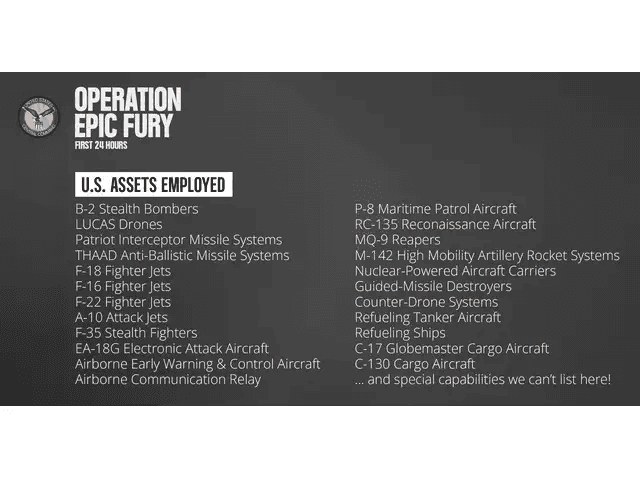
Based on the USCYBERCOM operational system and the latest developments in 2025, these special capabilities are likely to point to the following cyber warfare methods:
6.1 Industrial Control System (ICS) Attack Weapons
- Tactical Target: Uranium enrichment centrifuge control systems at Iran's underground nuclear facilities in Fordow and Natanz
- How it is attacked: By putting in a backdoor or zero-day vulnerability, embedding a similar Stuxnet malicious code that causes centrifuges to run at speed or to shut down abnormally, causing physical damage without the need for conventional bombing
- Impact: Paralyzing Iran's nuclear capabilities
6.2 Network-Electromagnetic Integration Suppression
- Collaborative equipment: EA-18G "Growler" Electronic Warfare Aircraft and Network Department Joint Action
- Operational Effect: Using AI-powered "Cognitive Electronic Warfare" to instantly analyze Iranian air defense systems (like the S-300 and Bavar-373). The system identifies their radar signals and generates precise interference to either blind the radar or trick it into seeing fake targets.
- Battlefield role: Opening up an "Electromagnetic Corridor" for the B-2 stealth bomber to ensure its penetration into the Iranian air defense network
6.3 Disable Command Communication Network
- Targets: Iranian Revolutionary Guard Corps (IRGC) command and control network, optical fibre communication nodes and satellite links
- Tactical Objective: To block high-level Iranian command over front-lines forces, delay decision-making on missile counterstrikes and create a "command vacuum"
6.4 AI-Driven Autonomous Network Agents
- Technical background: The US military has deployed "Autonomous Intelligent Cyber Agents"
- Scenario: During an air strike, an AI agent autonomously infiltrates Iran's power distribution system, financial networks, or transportation control systems, causing major cities to become partially paralysed, thereby causing social panic and internal unrest
8. Conclusion
Cyber warfare is no longer a supporting tool, it is the opening move. Operation Epic Fury has demonstrated that modern conflict is no longer decided solely by firepower, but by whoever controls the invisible layers of code, signal, and system. Central Command's phrase "cannot provide further details" is not just operational security; it is a glimpse into the architecture of sixth-generation warfare, where artificial intelligence, advanced stealth, hypersonic speeds, and automated action across air, land, and sea converge into something faster than any defense can respond to. The next war may begin with a line of code. And it may be over before anyone even realises it has started.
